Network security in manufacturing environments is essential for several reasons, which include safeguarding operations, protecting sensitive data, ensuring employee and equipment safety, complying with regulations, and maintaining a competitive edge. Below are the key areas where network security plays a critical role in the manufacturing industry:
1. Ensuring Continuity of Production Operations
Preventing Production Disruptions:
Network security is vital to prevent network attacks that could lead to failures in production systems. For example, if a virus or malware attacks the control system of automated production lines, it could cause severe disruptions, halting production processes and incurring significant financial losses. A real-world example would be an attack like the Stuxnet virus, which targeted industrial control systems and led to widespread damage in manufacturing plants.
Maintaining Supply Chain Stability:
Manufacturers often rely on seamless network connections with suppliers and partners. Any security breach in these networks could disrupt the exchange of critical information, such as inventory levels, shipment schedules, and production plans. This could lead to delays in raw material supplies and product deliveries, thereby disrupting the entire supply chain.

2. Protecting Data Assets
Preventing Commercial Espionage:
Manufacturing companies often possess sensitive intellectual property, such as design blueprints, proprietary processes, and manufacturing methods. Network security breaches can lead to the theft of this intellectual property, which could result in the loss of market advantage. For example, a factory’s design documents could be stolen and sold to competitors, undermining the company’s position in the market.
Safeguarding Customer Information:
Factories also store sensitive customer data, including orders, contact details, and financial transactions. A network breach exposing such data can damage the company’s reputation and lead to legal consequences. In the event of a data breach, regulatory bodies may impose heavy fines and the company could face lawsuits from affected customers. Therefore, robust network security measures are needed to protect both business and customer information.
3. Ensuring Employee and Equipment Safety
Protecting Employee Safety:
In modern, smart factories, many systems are automated and interconnected. A cyberattack that compromises security systems, such as fire suppression or emergency response protocols, could pose a direct threat to employees’ lives. For instance, an attack that disables an alarm system during a fire emergency could result in serious harm to employees.
Protecting Equipment Assets:
Malicious attacks can also damage valuable manufacturing equipment. For example, malware could control production equipment, forcing machines to run at unsafe speeds or under excessive loads, causing wear and tear, or even damaging them beyond repair. This could lead to costly downtime and repairs.
4. Meeting Compliance and Regulatory Requirements
Adhering to Industry Standards:
Certain industries, such as automotive manufacturing, have specific network security standards that manufacturers must follow. For instance, the automotive industry must comply with the ISO/SAE 21434 standard for cybersecurity in road vehicles. Failure to meet these standards could result in the company losing certifications, facing legal liabilities, or being prohibited from engaging in certain business practices.
Legal and Regulatory Compliance:
Various laws and regulations require manufacturers to protect sensitive data and ensure cybersecurity. For example, the General Data Protection Regulation (GDPR) in Europe mandates strict measures to protect personal data. Manufacturers that fail to adhere to such regulations can face severe financial penalties and damage to their brand’s reputation.
5. Maintaining Corporate Reputation and Market Competitiveness
Building a Positive Brand Image:
A strong focus on network security demonstrates that a company is responsible and trustworthy. Clients and partners feel more secure working with a manufacturer who takes cybersecurity seriously. For example, companies in sectors like pharmaceuticals or food manufacturing, where safety and compliance are paramount, will benefit from a robust security posture as it enhances their image.
Enhancing Market Trust:
Manufacturers that implement strong network security measures are more likely to attract new customers and business partners. A well-guarded digital infrastructure conveys reliability, increasing the company’s competitive edge in the marketplace. In contrast, failing to secure the network can result in lost business opportunities and damage to long-standing relationships.

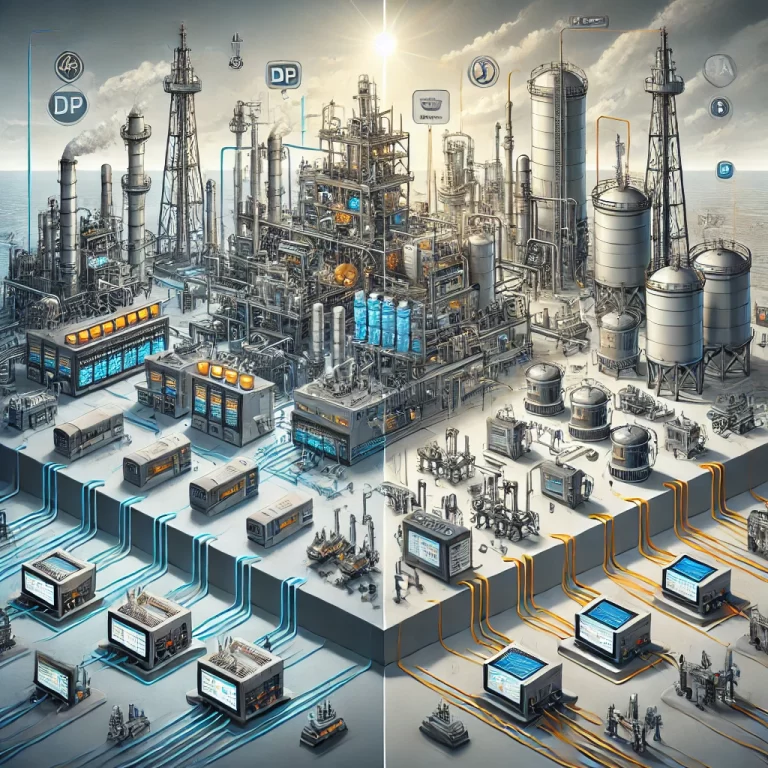
Commonly Used Network Security Devices in Manufacturing
To ensure a robust network security framework, manufacturers typically deploy a variety of devices and systems:
Firewalls:
Firewalls help isolate the factory’s internal network from external networks. By filtering inbound and outbound traffic based on pre-set security rules, firewalls prevent unauthorized access and mitigate cyber threats.Intrusion Detection and Prevention Systems (IDS/IPS):
IDS/IPS systems continuously monitor network traffic, analyze data packets, and detect suspicious behavior. If an intrusion is detected, the system can either alert security personnel or automatically take actions to block the threat.Security Gateways:
These gateways offer essential security functions like traffic management and access control. They also provide additional layers of protection such as anti-virus and anti-spam measures, ensuring that all data entering and leaving the network is clean and safe.Virtual Private Networks (VPNs):
VPNs create encrypted tunnels for secure communication between factory systems and remote users. This ensures that sensitive data transmitted over the network remains confidential and secure from potential interception.Security Information and Event Management (SIEM):
SIEM systems provide real-time monitoring and analysis of security events across the network. They aggregate data from various sources and provide security teams with insights, helping them respond to threats quickly.Network Access Control (NAC):
NAC solutions control access to the network by authenticating devices and users before granting permission. Unauthorized users or devices are blocked from accessing the network, reducing the risk of internal and external threats.Data Loss Prevention (DLP) Systems:
DLP systems monitor the flow of sensitive data across the network and prevent accidental or malicious data leakage. These systems can scan emails, file transfers, and other forms of communication for confidential information.Industrial Auditing Products:
These products use deep protocol inspection to monitor the integrity of industrial control networks, identifying irregularities and potential threats in real-time. They help in ensuring compliance and detecting early signs of cyberattacks in critical manufacturing systems.Bastion Hosts:
Bastion hosts provide secure access to critical systems by centralizing authentication and authorization. They act as a control point for monitoring operations and ensuring that only authorized personnel can access sensitive systems.

Conclusion
In today’s digital age, manufacturing plants face a growing range of cybersecurity threats that can disrupt operations, damage reputations, and result in financial losses. By prioritizing network security and implementing the right technologies, manufacturers can safeguard their operations, protect valuable data, and ensure compliance with legal and industry standards. With the right approach to cybersecurity, factories not only avoid costly disruptions but also position themselves as reliable and trustworthy partners in the market.
